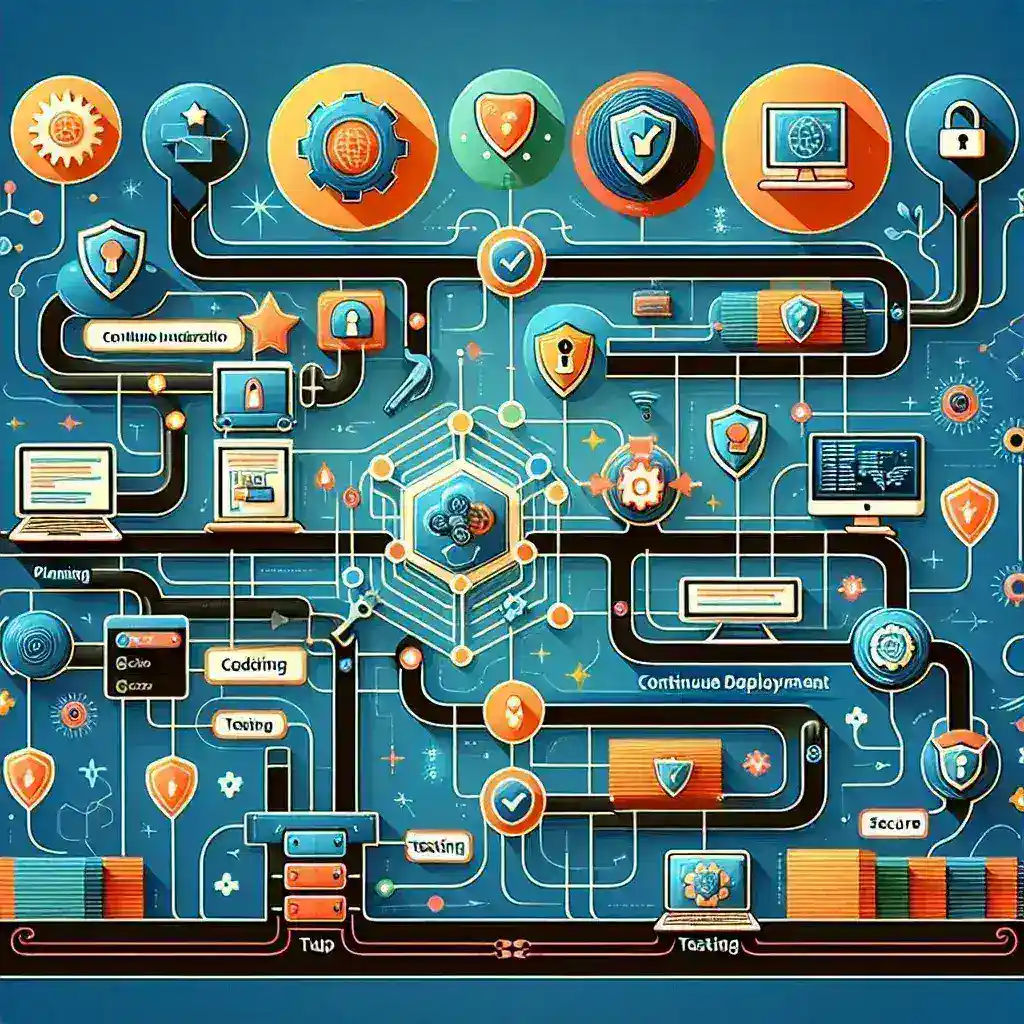
Understanding the Foundation of Secure Deployment Automation
In today’s fast-paced software development landscape, secure automated deployment pipelines have become the backbone of successful digital transformation initiatives. These sophisticated systems enable organizations to deliver code changes rapidly while maintaining the highest security standards throughout the entire software delivery lifecycle.
The evolution of deployment practices has shifted dramatically from manual, error-prone processes to sophisticated automated workflows that can handle thousands of deployments daily. However, with this increased automation comes the critical responsibility of ensuring that security remains paramount at every stage of the pipeline.
The Critical Components of Pipeline Security Architecture
Building a secure automated deployment pipeline requires careful consideration of multiple interconnected components that work together to create a fortress-like environment for your code delivery process.
Authentication and Authorization Frameworks
The first line of defense in any secure pipeline involves implementing robust authentication mechanisms. Multi-factor authentication (MFA) should be mandatory for all pipeline access points, while role-based access control (RBAC) ensures that team members can only interact with pipeline components relevant to their responsibilities.
Modern deployment pipelines leverage identity providers such as Active Directory, LDAP, or cloud-based identity services to centralize authentication. This approach not only enhances security but also simplifies user management across multiple tools and environments.
Code Integrity and Version Control Security
Protecting the source code repository forms the foundation of pipeline security. Implementing signed commits using GPG keys ensures that code changes can be traced back to verified developers. Branch protection rules prevent unauthorized modifications to critical branches, while automated scanning tools continuously monitor repositories for potential security vulnerabilities.
Version control systems should be configured with strict merge policies that require peer reviews and automated security checks before any code integration occurs. This multi-layered approach significantly reduces the risk of malicious code infiltrating the deployment pipeline.
Advanced Security Scanning and Vulnerability Assessment
Modern secure deployment pipelines incorporate multiple layers of automated security scanning that operate seamlessly within the continuous integration workflow.
Static Application Security Testing (SAST)
SAST tools analyze source code without executing it, identifying potential security vulnerabilities early in the development cycle. These tools can detect common security issues such as SQL injection vulnerabilities, cross-site scripting (XSS) flaws, and insecure cryptographic implementations.
Integration of SAST tools into the pipeline ensures that security analysis occurs automatically with every code commit, providing immediate feedback to developers about potential security concerns.
Dynamic Application Security Testing (DAST)
While SAST examines code at rest, DAST tools evaluate running applications to identify runtime vulnerabilities. These tools simulate real-world attacks against deployed applications, uncovering security issues that might not be apparent through static analysis alone.
Incorporating DAST into deployment pipelines typically occurs in staging environments where applications can be safely tested without impacting production systems.
Software Composition Analysis (SCA)
Modern applications heavily rely on third-party libraries and open-source components, making SCA an essential component of secure deployment pipelines. SCA tools inventory all dependencies and continuously monitor them for known vulnerabilities, license compliance issues, and potential security risks.
Automated dependency updates and vulnerability patching can be integrated into the pipeline workflow, ensuring that applications remain protected against newly discovered threats in third-party components.
Infrastructure Security and Environment Hardening
Securing the underlying infrastructure that supports deployment pipelines requires comprehensive planning and implementation of multiple security controls.
Container Security and Image Scanning
Containerized deployments have become the standard for modern applications, necessitating specialized security measures for container images and runtime environments. Container image scanning should occur at multiple points in the pipeline, including during image building, before deployment, and continuously in production.
Implementing container security policies that enforce resource limits, network segmentation, and access controls helps prevent potential container escape attacks and lateral movement within the infrastructure.
Network Segmentation and Micro-segmentation
Proper network architecture plays a crucial role in pipeline security. Network segmentation isolates different environments (development, staging, production) while micro-segmentation provides granular control over communication between individual services and components.
Software-defined networking (SDN) technologies enable dynamic security policies that can adapt to changing deployment patterns while maintaining strict security boundaries.
Secrets Management and Cryptographic Security
One of the most critical aspects of secure deployment pipelines involves the proper handling of sensitive information such as API keys, database credentials, and cryptographic certificates.
Centralized Secrets Management
Dedicated secrets management platforms provide secure storage, rotation, and distribution of sensitive credentials throughout the deployment pipeline. These systems ensure that secrets are never stored in plain text within code repositories or configuration files.
Integration with deployment tools allows for dynamic secret injection at runtime, eliminating the need to embed credentials in application code or deployment artifacts.
Certificate Management and PKI Integration
Public Key Infrastructure (PKI) integration enables automated certificate provisioning, renewal, and revocation throughout the deployment lifecycle. This automation reduces the risk of expired certificates causing service disruptions while maintaining strong cryptographic security.
Monitoring, Logging, and Incident Response
Comprehensive monitoring and logging capabilities provide visibility into pipeline operations and enable rapid detection of security incidents.
Security Information and Event Management (SIEM)
SIEM integration allows security teams to correlate pipeline events with broader security monitoring efforts. Automated alerting rules can trigger immediate responses to suspicious activities within the deployment infrastructure.
Audit Trails and Compliance Reporting
Detailed audit logs capture all pipeline activities, providing the documentation necessary for compliance with regulatory requirements such as SOX, GDPR, or industry-specific standards.
Automated compliance reporting tools can generate regular assessments of pipeline security posture, identifying areas for improvement and ensuring continuous adherence to security policies.
Best Practices for Implementation and Maintenance
Successfully implementing secure automated deployment pipelines requires adherence to established best practices and continuous improvement processes.
Security by Design Principles
Incorporating security considerations from the initial pipeline design phase ensures that security controls are built into the foundation rather than added as an afterthought. This approach results in more robust and maintainable security implementations.
Regular Security Assessments and Penetration Testing
Periodic security assessments help identify potential vulnerabilities in pipeline configurations and processes. Professional penetration testing can uncover sophisticated attack vectors that might not be apparent through automated scanning tools alone.
Team Training and Security Awareness
Human factors remain one of the most significant security risks in any technical system. Regular training programs ensure that development and operations teams understand security best practices and can recognize potential threats.
Future Trends and Emerging Technologies
The landscape of secure deployment pipelines continues to evolve with emerging technologies and changing threat landscapes.
Machine Learning and AI-Powered Security
Artificial intelligence and machine learning technologies are increasingly being integrated into deployment pipelines to provide advanced threat detection and automated response capabilities. These systems can identify anomalous patterns that might indicate security breaches or policy violations.
Zero Trust Architecture Integration
Zero trust security models are being adapted for deployment pipeline environments, requiring verification and validation of every component and interaction within the pipeline ecosystem.
This comprehensive approach to deployment pipeline security ensures that organizations can maintain rapid development velocity while protecting their most valuable digital assets. The investment in robust security measures pays dividends through reduced security incidents, improved compliance posture, and enhanced customer trust.
As software development practices continue to evolve, the importance of secure automated deployment pipelines will only increase. Organizations that prioritize pipeline security today will be better positioned to adapt to future challenges and maintain competitive advantages in an increasingly digital marketplace.